Veeam released their latest Data Trust and Resilience Report this week and there’s some very interesting stats that will make for some uncomfortable reading. You can get your copy here.
There’s a lot in the report, with some very vaulable data around cyber insurance, AI and more. But the first uncomfortable statistic is that most CIOs think their DR plan is solid, but the data says otherwise.
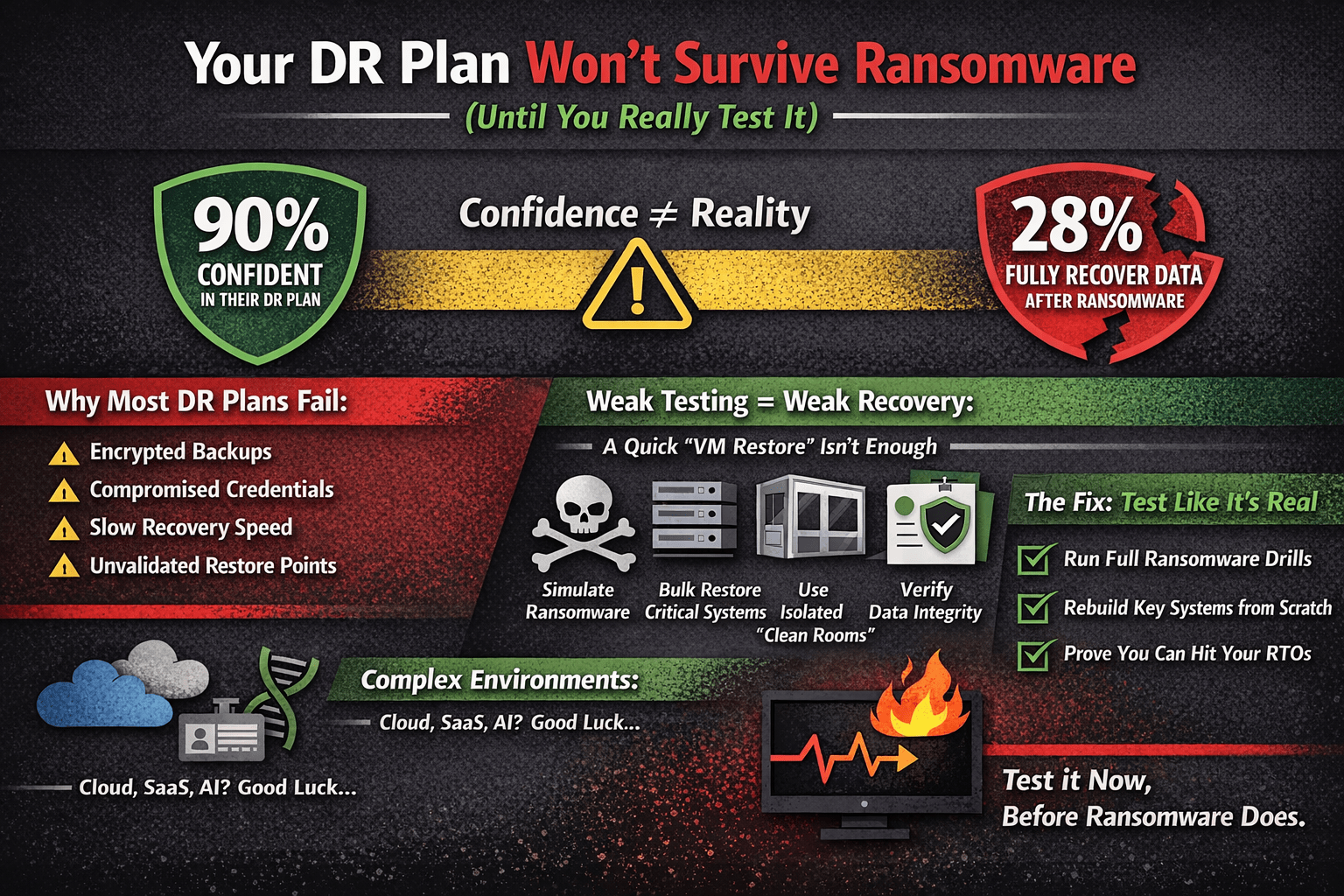
In their latest research, 90% of leaders are confident they’ll hit their RTOs—but when ransomware actually hits, only 28% fully recover their data .
That’s not a gap. That’s a disconnect.
The Technical Problem
This usually comes down to one thing: untested recovery paths.
On paper, everything looks fine:
- Backups are running
- Jobs are green
- Replication is in place
But in a real ransomware scenario, the failure modes stack up fast:
- Backup chains are partially encrypted
- Credentials used by backup software are compromised
- Immutability isn’t actually enforced end-to-end
- Restore points exist, but aren’t clean
- Recovery throughput can’t meet RTOs at scale
And the big one:
nobody has tested a full environment rebuild under pressure.
Testing (Properly) Is Where Most Shops Fall Down
A “DR test” in many environments means:
- Restoring a VM or two
- Checking a box for audit/compliance
That’s not recovery—that’s a demo.
Real testing should look more like:
- Simulated ransomware (including credential compromise)
- Bulk restore of tier-1 systems
- Isolated recovery environments (clean room)
- Verification of data integrity, not just restore success
If you’re not testing those, you don’t know if:
- Your backups are usable
- Your sequencing works (AD, DNS, apps)
- Your RTOs are even remotely achievable
Modern Environments Make It Worse
Throw in:
- Hybrid cloud
- SaaS dependencies
- Identity as the control plane
- AI/data pipelines
Now your recovery scope isn’t just VMs—it’s:
- Identities
- APIs
- Data flows you don’t fully track
Which explains why so many recoveries fail halfway through.
The Fix Is Boring (But Rare)
The orgs that actually recover well do a few things consistently:
- Test often, and break things on purpose. Build the muscle memory!
- Validate clean restore points (not just latest)
- Use immutability + separate security domains
- Measure recovery speed, not backup success
Bottom Line
If you haven’t:
- Simulated a ransomware attack
- Rebuilt critical services from scratch
- Proven you can hit RTOs under load
…then your DR plan isn’t validated.
It’s just assumed.
And ransomware is very good at testing assumptions.